Container Runtime Security 2026: Falco vs Tetragon vs Sysdig Secure vs Aqua Enforcer
Container runtime security compared for 2026 - Falco, Tetragon, Sysdig Secure, Aqua Enforcer, Prisma Defender, Tracee. eBPF-based threat detection, in-line blocking, MITRE ATT&CK coverage, performance overhead, and UAE compliance fit for Kubernetes production.
Container runtime security is the detection layer that catches what manifest and image scanners cannot: the actual behaviour of containers and nodes at runtime. A vulnerable image that got past Trivy. A malicious package that activates only post-deployment. A compromised sidecar making outbound connections. A privilege escalation via a kernel bug. All of these are runtime events - invisible to anything that looks only at cluster configuration.
This guide compares the 6 dominant container runtime security tools in 2026 - Falco, Tetragon, Sysdig Secure, Aqua Enforcer, Prisma Defender, and Tracee - on detection depth, in-line blocking capability, performance overhead, MITRE ATT&CK coverage, and fit for UAE enterprises under NESA, DESC ISR v3, and CBUAE compliance.
Why Runtime Security Is Non-Negotiable in 2026
Kubescape scans cluster configuration. Trivy Operator scans container images and manifests. Checkov scans IaC. None of these see what a container does. Runtime security fills that gap:
- A compromised dependency in an image that passed Trivy’s CVE scan because the vulnerability had no CVE yet - runtime security catches the malicious behaviour when the package activates
- A supply-chain-compromised base image where the malware triggers only in production conditions - runtime security catches the post-deployment activation
- A legitimate container running a malicious action because of input data exploitation (SQL injection escalating to RCE) - runtime security catches the shell spawn
- An insider-threat scenario where an authorized engineer exfiltrates data via a normal-looking container workload - runtime security catches the unexpected data flow
For UAE banks, fintechs, and regulated entities under CBUAE Article 13 or DESC ISR v3, “we scan images and manifests” is not a complete control. Inspectors increasingly ask about runtime detection specifically.
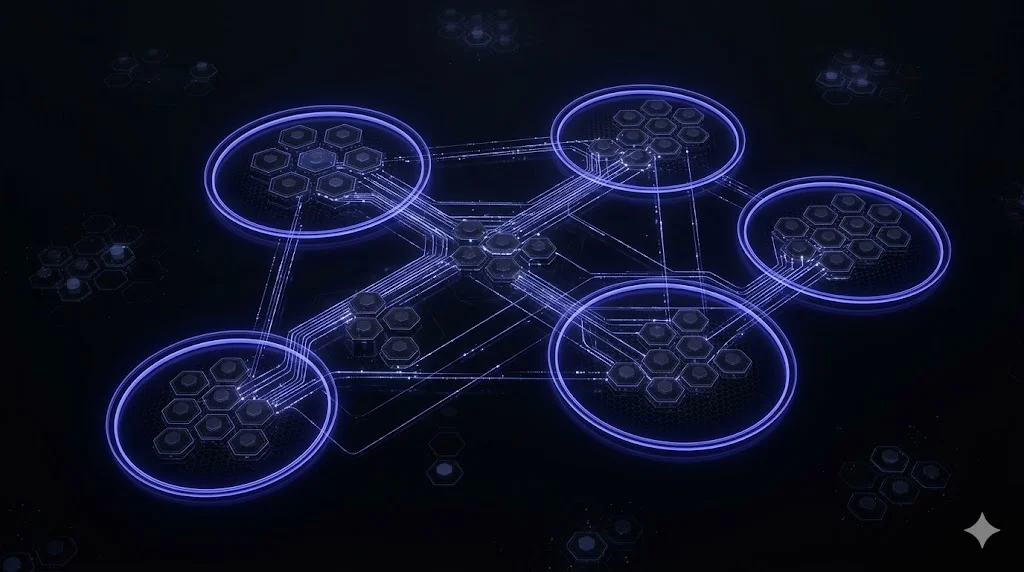
The Technology: eBPF Is The Enabler
All serious 2026 runtime security tools use eBPF (extended Berkeley Packet Filter) to observe kernel-level activity - syscalls, network packets, file access, process exec - without requiring kernel modules. eBPF is now the runtime-security standard for three reasons:
- Performance: eBPF programs run in kernel with JIT compilation, adding 1-5% CPU overhead typical vs 10%+ for legacy kernel-module approaches
- Safety: eBPF’s verifier prevents programs from crashing the kernel - reduces operational risk
- Portability: CO-RE (Compile Once, Run Everywhere) eBPF works across kernel versions, eliminating the per-distro compile burden
Falco, Tetragon, Tracee, and Sysdig all use eBPF. Older runtime tools with legacy kernel modules are end-of-life.
The 6 Tools
Falco - The CNCF-Graduated Default
Falco is the 2026 runtime security default. Originally created at Sysdig in 2016, donated to CNCF in 2018, graduated 2024. Production use at thousands of organizations.
- Architecture: eBPF probe on each node monitoring syscalls; rules engine evaluates events against declarative YAML rules
- Rule ecosystem: default rules plus community rule packs for MITRE ATT&CK for Containers, PCI DSS, HIPAA, NIST 800-190
- Integration: Falcosidekick fan-outs events to 70+ destinations (Slack, Teams, PagerDuty, Opsgenie, Elasticsearch, Splunk, Sentinel, Prometheus, Grafana, Kafka, NATS, AWS EventBridge, GCP PubSub, etc.)
- Enforcement: alerts-focused; in-line blocking requires integration with response automation or admission control
- License: Apache 2.0 (CNCF graduated)
Fit: any Kubernetes deployment needing runtime detection. Start here. The community, documentation, and rule ecosystem are unmatched.
Tetragon - The Cilium-Native Enforcer
Tetragon (Isovalent, open source, CNCF incubating) is the runtime security component of the Cilium ecosystem. Built for clusters running Cilium as CNI but works on any Kubernetes cluster.
- Architecture: eBPF probes with deep kernel-level observability - syscalls, network, file, process, memory
- Distinctive capability: native in-line enforcement via eBPF - can block syscalls, terminate processes, or drop network packets at kernel level before the action completes
- Policy model: TracingPolicy CRDs declaratively define what to observe and what to enforce
- Cilium integration: deep - when paired with Cilium CNI, Tetragon sees network policy violations in rich detail
- License: Apache 2.0
Fit: Cilium-native clusters. Organizations that need in-line enforcement (not just alerting). Teams willing to adopt newer tooling for deeper capability.
Sysdig Secure - The Commercial CNAPP Built Around Falco
Sysdig Secure is the commercial platform from Falco’s original sponsor. Built around Falco’s runtime engine but extends beyond:
- Centralized dashboards for findings across all clusters, clouds, workloads
- In-line blocking via Sysdig’s extensions to Falco (Falco OSS does not block)
- Deeper forensics - sysdig capture files for post-incident analysis
- CNAPP scope - CSPM, CIEM, container image scanning, IaC scanning on top of runtime
- Compliance frameworks - managed rule packs for PCI DSS, HIPAA, NIST, SOC 2, GDPR, plus customization
Fit: organizations wanting Falco’s runtime capability with commercial support, centralized governance, and a single CNAPP vendor. Mid-to-large enterprise.
Aqua Enforcer - The Kubernetes-First Commercial Runtime
Aqua Enforcer is the runtime component of Aqua Platform - the Kubernetes-first commercial CNAPP from the team behind Trivy OSS.
- Architecture: agent per node, with eBPF and custom runtime sensors
- In-line blocking: native, with policies covering process execution, network egress, file access, privilege escalation
- Deep Kubernetes-native integration with admission control, image scanning, and policy enforcement consolidated
- Compliance mapping across common frameworks
Fit: Kubernetes-first organizations, teams migrating from Trivy OSS to a commercial platform, enterprises where container and runtime security is the primary concern.
Prisma Defender - The Palo Alto Runtime Agent
Prisma Defender (Palo Alto Networks) is Prisma Cloud’s runtime protection agent, originally from the Twistlock acquisition.
- Architecture: agent per node with eBPF and process monitoring
- Scope: containers, Kubernetes, serverless functions, VMs
- Enforcement: in-line blocking, vulnerability-driven runtime policies, network micro-segmentation
- Integration with Prisma Cloud’s full CNAPP platform and Palo Alto’s broader security ecosystem
Fit: Palo Alto-aligned enterprises, defence-in-depth scenarios, organizations already on Prisma Cloud.
Tracee - The Forensics-Focused Tool
Tracee (Aqua Security, open source) is the eBPF-based runtime forensics and threat detection tool. Sibling project to Trivy Operator.
- Architecture: eBPF probes with detailed syscall and kernel-level capture
- Positioning: more forensics-focused than Falco’s alerting model - Tracee emphasizes post-incident investigation capabilities
- Signature coverage: known attack pattern signatures (MITRE ATT&CK) with emphasis on stealth detection
- Output: events to various sinks or to file for forensic analysis
Fit: organizations needing deep post-incident forensics. Less widely adopted than Falco for primary alerting; more niche.
Comparison Matrix
| Tool | CNCF / OSS | Detection | In-line Blocking | Performance | Ecosystem | Fit |
|---|---|---|---|---|---|---|
| Falco | Graduated / Apache 2.0 | Comprehensive | Alerts (via integrations) | 1-3% CPU | Largest | 2026 default |
| Tetragon | Incubating / Apache 2.0 | Deep kernel | Native eBPF | 1-4% CPU | Cilium-native | In-line enforcement |
| Sysdig Secure | Commercial | Comprehensive | Native | 2-5% CPU | Mature | Commercial Falco |
| Aqua Enforcer | Commercial | Strong K8s | Native | 2-5% CPU | Good | Kubernetes-first |
| Prisma Defender | Commercial | Comprehensive | Native | 3-6% CPU | Palo Alto | Defence-in-depth |
| Tracee | OSS Apache 2.0 | Signature-based | Limited | 1-3% CPU | Smaller | Forensics |
Rule Ecosystems and MITRE ATT&CK Coverage
Falco ships with default rules covering 40+ MITRE ATT&CK for Containers techniques. Community rule packs add coverage for:
- PCI DSS (cardholder data environment)
- NIST 800-190 (container security)
- HIPAA (healthcare)
- MITRE ATT&CK for Kubernetes (cluster-specific techniques)
- Cryptomining detection
- Kubernetes privilege escalation
- Container drift detection (changes to running container filesystem)
Commercial platforms ship similar but curated rule packs with support SLAs for rule updates.
For UAE compliance, pair Falco’s default rules with custom rules for:
- Unexpected access to UAE-specific data classifications (e.g., CBUAE customer data paths)
- Outbound connections to non-UAE destinations (egress control)
- Credential access patterns mapped to CBUAE Article 13 and NESA IA requirements
Performance Overhead: The Real Numbers
Real-world performance overhead on production Kubernetes clusters in 2026:
| Tool | Typical CPU | Typical memory per node | Notes |
|---|---|---|---|
| Falco (eBPF) | 1-3% | 150-300 MB | Well-tuned production |
| Tetragon | 1-4% | 200-400 MB | With enforcement policies |
| Sysdig Secure | 2-5% | 300-500 MB | Including all agents |
| Aqua Enforcer | 2-5% | 400-600 MB | Runtime + scanning |
| Prisma Defender | 3-6% | 500-800 MB | Full agent footprint |
| Tracee | 1-3% | 200-400 MB | Forensics capture adds overhead |
Rule quality matters enormously. A poorly-written rule that evaluates against millions of syscalls per second can 3-5x the reported numbers. Rule tuning is part of any runtime-security deployment.
Recommended Stacks by Maturity
Startup / small team (under 50 developers, single cluster)
- Falco + Falcosidekick routing to Slack
- Default rules + PCI DSS / NIST rule packs
- No in-line blocking initially; add later via Tetragon if needed
Annual cost: zero licences; operational overhead of rule tuning (~5 hours/month steady-state).
Mid-size enterprise (50-500 developers, multi-cluster)
- Falco + Falcosidekick routing to SIEM (Sentinel, Splunk, or Sumo Logic)
- Custom rules for organization-specific controls
- Tetragon for in-line enforcement on high-sensitivity namespaces
- DefectDojo for centralized findings aggregation
- Documented incident-response runbook for runtime events
Annual cost: zero licences for tools; operational ~20-40 hours/month for rule tuning + incident triage.
Regulated enterprise (UAE banks, fintechs, government)
- Falco + Falcosidekick to Sentinel or Splunk in UAE-resident tenant
- Custom rules mapped to CBUAE Article 13, NESA IA, DESC ISR v3 controls
- Commercial platform upgrade: Sysdig Secure, Aqua Platform, or Prisma Cloud for centralized governance, dashboards, compliance reporting, and 24x7 support
- Documented enforcement on critical rules (not just alerts)
- Annual rule-set review as part of compliance cycle
- Quarterly incident-response tabletop exercises
Annual cost: commercial platform licence USD 100-400k + operational investment.
Integrating Runtime With CI/CD and Admission
Runtime security is the third layer of a three-gate security model:
- Pre-merge (CI): SAST, SCA, IaC, secrets, manifest scanning (see our Snyk alternatives, IaC scanning, secrets scanners, K8s scanners posts)
- Admission (deployment): OPA/Gatekeeper or Kyverno validating manifests, enforcing image signatures via Cosign/Sigstore, blocking non-compliant pods
- Runtime: Falco / Tetragon / commercial platform detecting behaviour
Each layer catches what the previous missed. Runtime security alone is insufficient (you want to prevent bad deployments, not just detect them). CI and admission alone are insufficient (they cannot see post-deployment behaviour). All three together form defence-in-depth.
UAE Compliance: What Inspectors Expect
For NESA, DESC ISR v3, CBUAE Article 13, and NCA ECC audit evidence on runtime security:
- Tool deployment - documented runtime tool running on every production node
- Rule inventory - current ruleset with mapping to threat categories and compliance frameworks
- Alert routing - events flowing to SIEM with documented retention (NESA: 1 year minimum; CBUAE: 5 years for banks)
- Incident disposition - every detected event triaged as true positive / false positive / noise with documented response
- Performance monitoring - evidence the tool is actively running (uptime, event volume, resource usage)
- Periodic review - quarterly review of detected events and rule-set tuning
- Incident-response integration - runbook for escalation when runtime tool detects high-severity events
- Data residency - for commercial platforms, confirm SaaS control plane region; for OSS, verify no data leaves UAE-resident clusters
OSS stack (Falco + Falcosidekick + Sentinel/Splunk in UAE tenant) produces all of this evidence natively. Commercial platforms make the workflow smoother but add residency attestation as a pre-procurement step.
How NomadX Kubernetes Delivers
NomadX Kubernetes runs container runtime security deployment engagements as fixed-scope sprints:
- 5-day Runtime Security Assessment - evaluates current runtime detection coverage, identifies gaps, benchmarks against MITRE ATT&CK for Containers, produces prioritized deployment roadmap
- 2-4 week Runtime Security Implementation - deploys Falco + Falcosidekick + SIEM integration; authors custom rules for UAE compliance controls; trains engineering and SOC teams
- Ongoing monthly retainer - rule tuning, event triage support, quarterly tabletop exercises, compliance evidence preparation
For CBUAE-regulated banks, engagements include explicit mapping of runtime rules to Article 13 and Annex II controls with inspection-ready documentation.
Book a free 30-minute discovery call to scope your Kubernetes runtime security engagement with a NomadX Kubernetes engineer.
Frequently Asked Questions
What is container runtime security?
Container runtime security detects and (optionally) blocks suspicious behaviour inside running containers and the Kubernetes nodes hosting them - things a manifest scanner cannot see because the threat doesn't exist at deployment time. Typical detections: a shell process spawning inside a container, an unexpected outbound network connection to a suspicious domain, a file write to sensitive paths like /etc/passwd, privilege escalation via setuid, or cryptomining indicators. Runtime security complements manifest and image scanning, which catch issues at deployment time.
Falco vs Tetragon - which should I use?
Both are eBPF-based CNCF projects with overlapping scope. Falco is CNCF-graduated and more mature (originally launched 2016); rich rule ecosystem; alerts-focused; easy to deploy. Tetragon is newer (Isovalent/Cilium), with deeper kernel-level observability and native in-line blocking via eBPF (Falco primarily alerts). For Cilium-native clusters, Tetragon is the natural choice. For broader deployment or teams wanting the most mature alerting-focused runtime detector, Falco remains the default.
Does Falco block attacks or just alert?
Falco is primarily alert-focused. When a rule fires, Falco emits an event that you route to Slack / PagerDuty / Sentinel / any SIEM via Falcosidekick. Blocking is not native - it requires integration with an admission controller or response system. For in-line blocking (preventing the bad syscall or network connection), Tetragon provides native eBPF enforcement, as do commercial platforms like Aqua Enforcer, Prisma Defender, and Sysdig Secure.
What is the performance overhead of Falco?
Falco's eBPF probe adds approximately 1-5% CPU overhead on typical Kubernetes nodes depending on syscall volume and active rule complexity. The legacy kernel module driver (Falco's original architecture) has higher overhead but is deprecated. eBPF probe is the 2026 default. Rule tuning matters - poorly-written rules that match millions of syscalls per second degrade performance; well-tuned production rules stay under 3% CPU.
Is Sysdig Secure just commercial Falco?
Sysdig is Falco's original commercial sponsor and core maintainer - Falco's runtime engine is what Sysdig Secure is built on. Sysdig Secure extends beyond Falco OSS with: centralized dashboards, in-line blocking, deeper syscall forensics, cloud posture management (CSPM, CIEM), container image scanning, and IaC scanning - essentially a full CNAPP built around Falco's runtime story. For teams running Falco OSS and wanting commercial support, Sysdig is the natural upgrade path.
Do I need runtime security if I have Kubescape and Trivy Operator?
Yes. Kubescape scans cluster config and workload posture - what the manifest says. Trivy Operator scans container images and manifests continuously - what is configured. Neither sees what the container does at runtime. A malicious container that passed image scanning (because its malicious behaviour only activates post-deployment) will not be caught by Trivy Operator or Kubescape. Runtime security is the detection layer that catches behaviour, not configuration. Defence-in-depth requires all three.
Which container runtime security tool satisfies NESA and DESC compliance?
All serious runtime tools satisfy the 'continuous monitoring and detection' requirements of NESA IA, DESC ISR v3, and CBUAE Article 13 when deployed and operational. The compliance critical criteria are: (1) documented rule set with mapping to threat categories; (2) alerts routed to SIEM with retention; (3) incident-response runbook for detected events; (4) performance monitoring showing the tool is running; (5) periodic review of detected events. Falco + Falcosidekick + Sentinel/Splunk/DefectDojo produces all of this. Commercial platforms simplify the evidence-collection workflow.
Does runtime security work on Kubernetes in sovereign clouds (Core42, Stargate UAE)?
Yes. Falco, Tetragon, and Tracee are all OSS tools that run inside the Kubernetes cluster - no external dependencies, no data sent to vendor control planes. They work identically on Core42, Stargate UAE, Azure UAE North, AWS me-central-1, GCP, OCI, or on-premises. For the strictest interpretations of NESA and CBUAE data residency where no security telemetry can leave the country, OSS runtime tools running in-cluster are the cleanest residency story.
Complementary NomadX Services
Get Started for Free
We would be happy to speak with you and arrange a free consultation with our Kubernetes Expert in Dubai, UAE. 30-minute call, actionable results in days.
Talk to an Expert