Kubernetes Security Scanners 2026: Kubescape vs Trivy Operator vs Falco (and 6 More)
Kubernetes security scanners compared - Kubescape, Trivy Operator, Falco, Kube-bench, Kubesec, Starboard, Wiz, Prisma Cloud, Aqua. Cluster, workload, and runtime coverage with CIS / NSA / DISA benchmarks, runtime detection, and UAE compliance fit.
Kubernetes security scanning in 2026 is no longer about running a single tool against a cluster once a quarter. Production Kubernetes security splits into three distinct domains - cluster configuration posture, workload posture, and runtime behaviour - and a mature DevSecOps programme needs a scanner (or a consolidating platform) in each.
This guide compares the 9 tools most UAE and GCC teams should be evaluating in 2026: the CNCF open-source stack (Kubescape, Trivy Operator, Falco, Kube-bench, Kubesec, Starboard) and the three dominant commercial CNAPPs (Wiz, Prisma Cloud, Aqua Platform). It covers what each scanner actually checks, where each fits in a continuous pipeline, and how they map to UAE compliance requirements.
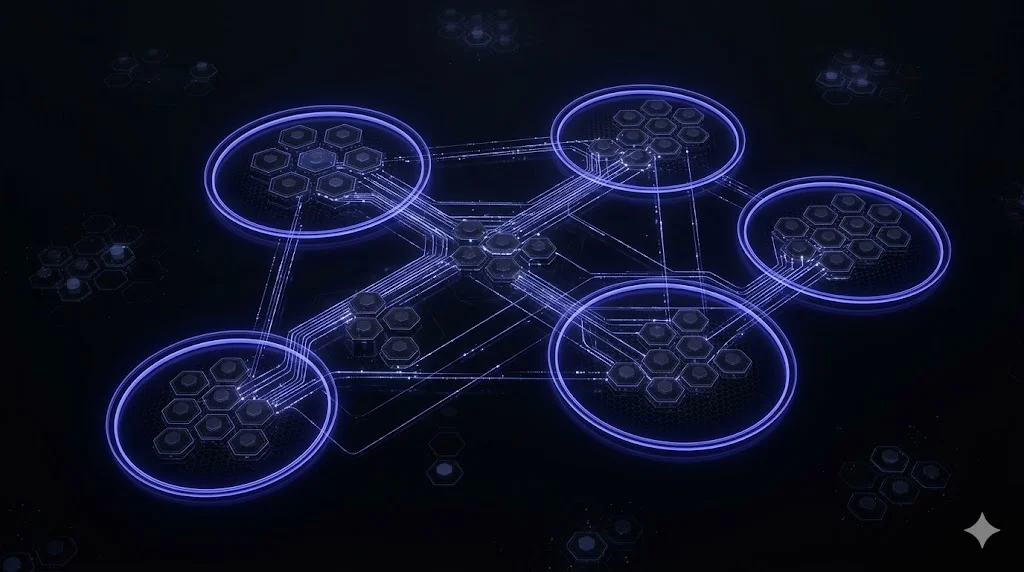
The Three Domains of Kubernetes Security Scanning
Any serious conversation about Kubernetes security scanners has to start with a clean split of what gets scanned:
Cluster configuration posture - is the control plane hardened? Are API server flags safe? Is etcd encrypted and access-controlled? Is RBAC least-privilege? Are network policies in place? CIS Kubernetes Benchmark and the NSA-CISA Kubernetes Hardening Guide cover this domain. Kubescape, Kube-bench, and Kubesec are the canonical scanners.
Workload posture - are the images running in the cluster free of known CVEs? Are pod specs avoiding privileged mode and host namespaces? Are secrets mounted appropriately? Are admission rules enforcing pod security standards? Trivy Operator and Starboard (its predecessor) are the open-source leaders.
Runtime behaviour - is a container doing something unexpected right now? Is a pod spawning shells, connecting to crypto-mining pools, tampering with files outside its scope? Falco is the CNCF-graduated open-source answer; commercial platforms add their own runtime defenders (Prisma Defender, Aqua Enforcer, Wiz runtime sensors).
A single tool that handles all three domains deeply does not exist in the open-source world. Commercial CNAPPs (Wiz, Prisma Cloud, Aqua) consolidate all three but at USD 200k+ annual licence cost for mid-size clusters.
Cluster Configuration Scanners
Kubescape (CNCF, open source) is the 2026 default. It ships with frameworks for CIS Kubernetes Benchmark, NSA-CISA Hardening Guide, MITRE ATT&CK for Containers, SOC 2, and custom framework authoring via YAML. It runs as a CLI (kubescape scan framework nsa) or as an in-cluster operator for continuous assessment, emits JSON / SARIF for CI gating, and has a hosted web UI (ARMO Platform) for centralized management. Fast to adopt - scanning a typical cluster takes under 2 minutes.
Kube-bench (Aqua Security, open source) runs the CIS Kubernetes Benchmark checks as a native Kubernetes Job. Narrower scope than Kubescape but the CIS output is authoritative - if your auditor wants “CIS Kubernetes Benchmark v1.10 results”, Kube-bench is the reference implementation. Use alongside Kubescape when specific CIS evidence matters.
Kubesec (ControlPlane, open source) scores individual Kubernetes resource manifests (pods, deployments, daemonsets) against security best practices - privileged mode, host namespace access, securityContext settings, etc. More of a CI-time linter than a cluster auditor. Pairs well with kubectl and GitOps workflows.
Starboard (Aqua Security, deprecated) was the predecessor to Trivy Operator. Deprecated - do not adopt for new clusters; Trivy Operator is the successor.
Practical pick: Kubescape as cluster-posture default. Add Kube-bench if CIS-specific audit evidence is required. Add Kubesec as a pre-deployment linter in CI.
Workload Posture Scanners
Trivy Operator (Aqua Security, open source) is the dominant workload scanner in 2026. Deployed as a Kubernetes Operator, it continuously scans:
- Container images for known CVEs across OS packages and language dependencies
- Pod configurations against pod security standards, CIS benchmarks, and custom policies
- Secrets exposed in pod specs or environment variables
- RBAC permissions for over-permissive roles, cluster-admin usage, wildcards
- Cluster compliance via bundled CIS checks
Results surface as Kubernetes CRDs (VulnerabilityReport, ConfigAuditReport, ExposedSecretReport, RbacAssessmentReport, ClusterComplianceReport). These feed naturally into Prometheus metrics, Grafana dashboards, Slack notifications via Alertmanager, or aggregation platforms like DefectDojo.
Checkov (Prisma Cloud, open source) covers Kubernetes manifest scanning as part of its broader IaC platform - useful if you’re already running Checkov for Terraform / CloudFormation and want Kubernetes coverage in the same scanner.
Practical pick: Trivy Operator for continuous in-cluster workload scanning, Checkov for pre-deployment manifest scanning in CI.
Runtime Detection
Falco (CNCF graduated, open source) is the runtime detection standard for Kubernetes. It uses eBPF (or legacy kernel module) to monitor Linux syscalls on each node and applies declarative rules to detect suspicious behaviour:
- Shell spawned inside a container
- Unexpected outbound network connections
- File writes to sensitive paths (
/etc/passwd,/proc,/sys) - Privilege escalation (setuid, capability changes)
- Cryptomining indicators
- Known attack patterns from MITRE ATT&CK
Falco ships with default rule packs and custom rules are authored in YAML. Findings emit as events - route them to Falcosidekick for fanout to Slack, Teams, PagerDuty, OpenSearch, or a SIEM.
Tetragon (Isovalent, open source) is an eBPF-based runtime security tool overlapping Falco’s scope with deeper kernel-level observability. Younger than Falco, with Cilium-native integration. Worth evaluating alongside Falco for 2026 deployments.
Tracee (Aqua Security, open source) is another eBPF-based runtime forensics tool - heavier, more forensics-focused than Falco’s alerting model.
Practical pick: Falco for alerting-focused runtime detection. Evaluate Tetragon if on Cilium. Tracee for deep forensics after an incident.
Commercial CNAPPs
Wiz has become the fastest-growing CNAPP in 2026 on the strength of its agentless cluster discovery and cloud-context-aware risk prioritization. It pulls a snapshot of cluster state via cloud APIs and produces a unified risk view across cluster config, workloads, cloud resources, and identity. Adds runtime sensors for behaviour detection. Fast to deploy, rich UX, expensive.
Prisma Cloud (Palo Alto) is the most comprehensive CNAPP - deepest integrated runtime protection via Prisma Defender agents, strong compliance-framework coverage, heavy operational footprint. Well-suited for regulated enterprises that already run Palo Alto firewalls and want one security vendor across perimeter + cloud + cluster.
Aqua Platform is the commercial successor to Trivy / Trivy Operator OSS. Deepest Kubernetes-native focus among the commercial CNAPPs, with the runtime Enforcer product adding policy-based blocking of suspicious actions. Natural upgrade path for teams already running Trivy at scale.
Practical pick: Wiz if speed to value matters and runtime gaps can be covered incrementally. Prisma Cloud for defence-in-depth in heavily regulated environments. Aqua for Kubernetes-first organizations ready to upgrade from OSS.
Comparison Table
| Scanner | Domain | Open Source | Runtime | Best For |
|---|---|---|---|---|
| Kubescape | Cluster + workload | Yes (CNCF) | Continuous | 2026 default cluster posture |
| Kube-bench | Cluster (CIS) | Yes | On-demand | CIS-specific audit evidence |
| Kubesec | Workload manifests | Yes | CI-time | Pre-deployment linting |
| Trivy Operator | Workload | Yes | Continuous | 2026 default workload scanner |
| Checkov | IaC + K8s manifests | Yes | CI-time | Multi-IaC + K8s coverage |
| Falco | Runtime | Yes (CNCF graduated) | Continuous | Runtime threat detection |
| Tetragon | Runtime | Yes | Continuous | Cilium-native runtime |
| Tracee | Runtime forensics | Yes | On-demand | Post-incident forensics |
| Wiz | CNAPP | No | Yes | Fast-to-deploy agentless CNAPP |
| Prisma Cloud | CNAPP | No | Yes | Deep runtime + compliance |
| Aqua Platform | CNAPP | No | Yes | K8s-native commercial upgrade |
| Starboard | Workload | Yes (deprecated) | - | DO NOT ADOPT - use Trivy Operator |
The 2026 Open-Source Reference Stack
For UAE and GCC teams running Kubernetes in production and needing continuous security without an enterprise CNAPP licence:
- Kubescape as the in-cluster posture operator, scanning against CIS + NSA frameworks
- Trivy Operator as the continuous workload scanner
- Falco with Falcosidekick for runtime detection routed to Slack / PagerDuty / SIEM
- Kube-bench run as a quarterly Job for authoritative CIS audit evidence
- Checkov in CI for pre-deployment manifest and IaC scanning
- OPA/Gatekeeper or Kyverno as the admission controller enforcing policy-as-code
- DefectDojo as the findings aggregator if scanner sprawl becomes hard to manage
- Prometheus + Grafana for metrics from Trivy Operator and Falco
This stack runs entirely inside UAE-resident clusters (residency by default), produces machine-readable findings for compliance reports, and enforces policy at admission time rather than reporting violations after the fact.
UAE Compliance Mapping
For NESA, DESC ISR v3, CBUAE Article 13, and NCA ECC (KSA cross-border) audit requirements, the relevant capabilities:
- Documented control baselines - Kubescape and Kube-bench produce explicit CIS / NSA control-by-control results suitable for auditor inspection.
- Continuous assessment - Trivy Operator and Kubescape-in-cluster run continuously, so evidence is always current (not just an annual snapshot).
- Runtime threat detection - Falco satisfies “ability to detect and respond to anomalous activity” controls in most frameworks.
- Segregation of duties - scanner findings should route into a system separate from where remediation happens (DefectDojo plus your ticketing system works).
- Data residency - all of the open-source tools run inside your cluster. Commercial CNAPPs need explicit UAE data-residency attestation for control planes.
For CBUAE-licensed banks, expect inspectors to ask for: scanner deployment evidence, finding disposition records, remediation SLAs, exception approvals, and quarterly compliance reports. The open-source stack supports all of this with DefectDojo and Grafana.
Integrating Scanners into Continuous DevSecOps
A mature continuous DevSecOps pipeline runs scanners at three gates:
Pre-merge (CI): Checkov and Kubesec validate manifests. Trivy scans images. Fail the build on critical findings.
Admission (cluster ingress): OPA/Gatekeeper or Kyverno enforces the policy - no images without scan attestation, no privileged pods, no missing resource limits, no non-UAE regions.
Runtime (continuous): Trivy Operator scans every running workload. Falco alerts on suspicious behaviour. Kubescape continuously assesses cluster posture. Findings route to Slack / Teams / PagerDuty and into SIEM for correlation.
This three-gate model is the practical realization of shift-left + shift-right security. Scanners alone do not secure Kubernetes - enforcement at admission and detection at runtime are what prevent compromise.
How NomadX Kubernetes Delivers
NomadX Kubernetes runs Kubernetes security hardening engagements that deploy and tune this entire stack - or migrate existing cluster-security tooling to the 2026 reference. Fixed-scope deliveries:
- 5-day K8s Security Assessment - scans against CIS, NSA, MITRE ATT&CK; produces prioritized hardening roadmap
- 3-4 week K8s Security Hardening Sprint - deploys Kubescape + Trivy Operator + Falco + OPA/Gatekeeper; maps findings to CIS/NSA/NESA/DESC control evidence; trains engineering team
- Monthly K8s Security Retainer - ongoing rule tuning, vulnerability triage, compliance evidence preparation, and support for quarterly audits
Book a free 30-minute discovery call to scope your Kubernetes security scanner deployment with a NomadX Kubernetes engineer.
Frequently Asked Questions
What is the best Kubernetes security scanner in 2026?
No single scanner covers all three domains - cluster configuration, workload posture, and runtime behaviour. The open-source 2026 default stack: Kubescape for CIS and NSA cluster hardening, Trivy Operator for continuous image and manifest scanning, Falco for runtime threat detection, and Kube-bench for CIS Kubernetes Benchmark deep audit. Commercial equivalents (Wiz, Prisma Cloud, Aqua) consolidate these into a single platform with centralized reporting at substantial licence cost.
What is Kubescape?
Kubescape is a CNCF open-source Kubernetes security platform that scans clusters against CIS Kubernetes Benchmark, NSA-CISA Kubernetes Hardening Guide, MITRE ATT&CK for Containers, and custom frameworks. It runs as a CLI for ad-hoc scans or as an in-cluster operator for continuous assessment. Kubescape produces JSON / SARIF findings that integrate into CI/CD and offers a web UI (ARMO Platform) for centralized reporting. Strong 2026 choice for cluster-level posture management.
What does Trivy Operator scan for?
Trivy Operator (Aqua Security, open source) continuously scans running workloads in a Kubernetes cluster for: (1) vulnerable container images (CVE detection), (2) misconfigured workloads (pod security, missing probes, privileged containers), (3) exposed secrets in pod specs, (4) insecure RBAC permissions, (5) non-compliant cluster configurations against CIS benchmarks. Findings are surfaced as Kubernetes CRDs (VulnerabilityReport, ConfigAuditReport, etc.) and can feed into DefectDojo, Prometheus, or Grafana.
What is Falco used for?
Falco is a CNCF graduated open-source runtime security tool that detects suspicious behaviour inside running containers and nodes. It monitors Linux syscalls via eBPF and applies rules to flag: shell-in-container, unexpected network connections, file-system tampering, privilege escalation, cryptomining indicators, and compliance violations. Falco ships with pre-built rule packs for MITRE ATT&CK, PCI DSS, and HIPAA contexts. It is the runtime detection layer complementing Kubescape and Trivy Operator.
Kube-bench vs Kubescape - which should I use?
Kube-bench is narrower and deeper on CIS Kubernetes Benchmark - it runs the CIS checks natively as a Kubernetes Job and produces precise compliance output. Kubescape covers CIS plus NSA, MITRE ATT&CK, and custom frameworks with a single tool. For 2026 cluster posture management, Kubescape is the broader choice; Kube-bench remains useful when you need CIS-only evidence for a specific auditor who expects CIS v1.10 results. Many teams run both.
What is the difference between Kubescape and Trivy Operator?
Kubescape focuses on cluster-level posture - the API server, etcd, scheduler, controller-manager, RBAC, network policies. Trivy Operator focuses on workload-level posture - images, manifests, secrets in pods, container configurations. They are complementary, not competing. Deploy both: Kubescape for cluster hardening against CIS / NSA, Trivy Operator for continuous workload scanning. Commercial platforms (Wiz, Prisma, Aqua) combine these concerns into one dashboard.
How do Wiz, Prisma Cloud, and Aqua compare for Kubernetes security?
All three are enterprise CNAPP platforms covering cluster config + workload posture + runtime + cloud context. Wiz leads on agentless speed-of-adoption and cloud-context-aware prioritization. Prisma Cloud (Palo Alto) has the deepest integrated runtime protection via Prisma Defender. Aqua Platform is the closest commercial upgrade path from Trivy OSS with strongest Kubernetes-native focus. Pricing scales with node count and cloud workload count - expect USD 200k+ annually for mid-size GCC enterprises.
Which Kubernetes security scanners satisfy NESA and DESC compliance?
For UAE compliance evidence, scanners must produce machine-readable findings, map to recognized frameworks (CIS, NSA, MITRE ATT&CK, PCI DSS), and run inside the UAE-resident cluster (not SaaS). Kubescape + Trivy Operator + Falco + Kube-bench satisfy these criteria by default - all run as in-cluster workloads. Commercial SaaS tools (Wiz, Prisma Cloud) need residency attestation for their control planes. For DESC ISR v3 audits, expect inspectors to ask for scanner configuration, finding disposition, and remediation evidence.
Complementary NomadX Services
Get Started for Free
We would be happy to speak with you and arrange a free consultation with our Kubernetes Expert in Dubai, UAE. 30-minute call, actionable results in days.
Talk to an Expert